Securing Sensitive Information in Government Offices: A Comprehensive Guide
In the modern digital age, the protection of sensitive information has become paramount, especially within government offices. Government agencies worldwide are entrusted with confidential data that ranges from national security secrets to citizens' personal information. Therefore, it is imperative that they employ robust security measures to safeguard this data from unauthorized access, breaches, and cyber threats. This article, brought to you by Templeton Safes, explores the importance of securing sensitive information in government offices and provides a comprehensive guide to achieving this crucial goal.
The Stakes Are High
Government offices are entrusted with a wide array of sensitive information that, if compromised, can have profound consequences. These may include:
-
National Security: Governments handle classified information related to national security, defense strategies, and intelligence. A breach in this data could jeopardize the safety and sovereignty of a nation.
-
Personal Records: Government agencies often store personal records of citizens, including social security numbers, medical histories, and financial information. The exposure of such data can lead to identity theft and financial fraud.
-
Policy Formulation: Confidential information is vital for shaping policies and legislation. Leaked documents can disrupt governance and national decision-making.
-
International Relations: Diplomatic cables and sensitive correspondence with foreign governments are crucial for maintaining international relations. Unauthorized access to such information can damage diplomatic ties.
-
Law Enforcement: Police and investigative agencies handle sensitive case files, informant data, and evidence. Breaches can compromise ongoing investigations and put lives at risk.
Given these high stakes, it is evident that securing sensitive information within government offices is of paramount importance. Let's delve into the strategies and best practices to achieve this goal.
1. Establish a Strong Information Security Policy
A robust information security policy is the cornerstone of safeguarding sensitive data within government offices. This policy should encompass:
-
Data Classification: Categorize data based on its sensitivity and importance, allowing for different levels of security measures.
-
Access Controls: Implement strict access controls, ensuring that only authorized personnel can access sensitive information.
-
Encryption: Encrypt sensitive data both in transit and at rest to protect it from eavesdropping and theft.
-
Password Policies: Enforce strong password policies, including regular password changes and multifactor authentication.
-
Data Backup: Regularly back up sensitive data to ensure that it can be recovered in case of data loss or ransomware attacks.
-
Incident Response Plan: Develop a comprehensive incident response plan to address data breaches promptly and effectively.
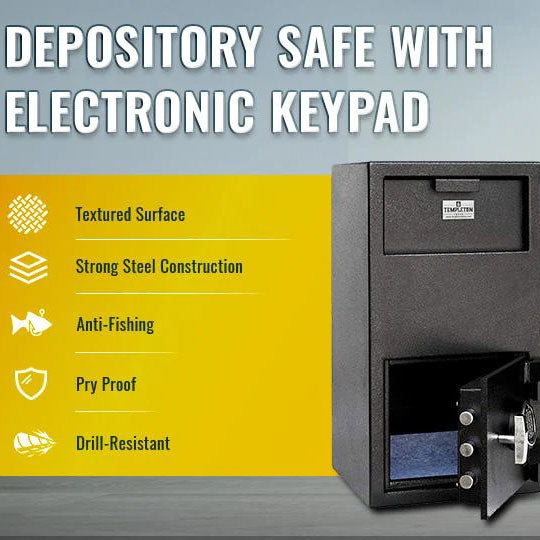
2. Secure Physical Access: Investing In Security Safes
In the pursuit of securing sensitive information in government offices, investing in high-quality security safes is a strategic decision that can significantly enhance data protection.
- Protection Against Physical Threats: While digital security measures are essential, physical threats cannot be ignored. Security safes provide an additional layer of defense against theft, vandalism, and unauthorized access by physical intruders.
- Secure Storage of Physical Documents: Many government offices still rely on physical documents for certain operations. Security safes are the ideal solution for storing confidential documents, sensitive records, classified information, and backup copies.
- Asset Protection: In addition to protecting sensitive information, security safes are excellent for safeguarding valuable assets such as electronic devices, weapons, evidence, and precious items.
3. Employee Training and Awareness
Government employees play a critical role in data security. It's imperative to provide regular training and raise awareness about cybersecurity:
-
Phishing Awareness: Train employees to recognize phishing attempts and avoid clicking on malicious links or downloading suspicious attachments.
-
Social Engineering: Educate staff about the risks of social engineering tactics and the importance of verifying the identity of individuals requesting sensitive information.
-
Insider Threats: Address the possibility of insider threats by promoting a culture of trust and accountability while monitoring employee actions when necessary.
-
Reporting Mechanisms: Establish clear channels for reporting security incidents or suspicious activities.
4. Implement Robust Network Security
With the increasing reliance on digital systems, network security is paramount for government offices:
-
Firewalls and Intrusion Detection Systems (IDS): Install firewalls to filter incoming and outgoing network traffic and employ IDS to detect and respond to suspicious network activities.
-
Regular Updates and Patch Management: Keep all software and operating systems up to date with the latest security patches to mitigate vulnerabilities.
-
Network Segmentation: Segment networks to limit lateral movement for potential attackers.
-
Security Audits and Vulnerability Assessments: Conduct regular security audits and vulnerability assessments to identify and address weaknesses in the network infrastructure.
5. Secure Mobile Devices and Remote Work
In today's flexible work environments, mobile devices and remote work have become common. Secure these aspects to prevent data breaches:
-
Mobile Device Management (MDM): Implement MDM solutions to control and secure mobile devices used by government employees.
-
Remote Access Security: Use secure VPNs and encrypted connections for remote access to government systems and data.
-
Bring Your Own Device (BYOD) Policies: If applicable, establish strict BYOD policies to ensure personal devices used for work do not compromise data security.
6. Data Encryption and Secure Communication
Ensure that all communication channels are secure, both within the office and when communicating externally:
-
Email Encryption: Use encryption for email communication, especially when sending sensitive documents or information.
-
Secure File Transfer: Implement secure file transfer protocols for sharing sensitive data, both internally and externally.
-
Secure Collaboration Tools: Choose collaboration and messaging tools that prioritize security and end-to-end encryption.
7. Regular Security Audits and Testing
Continuous monitoring and assessment of security measures are essential to stay ahead of evolving threats:
-
Penetration Testing: Conduct regular penetration testing to identify vulnerabilities in your systems and networks.
-
Security Audits: Perform comprehensive security audits to ensure compliance with security policies and regulations.
-
Security Awareness Programs: Keep employees informed about the latest security threats and best practices through regular training and awareness programs.
8. Data Destruction and Disposal
When sensitive data is no longer needed, ensure it is properly destroyed to prevent unauthorized access:
-
Shredding: Use secure shredding services for physical documents.
-
Data Wiping: Use secure data wiping software to remove all traces of data from electronic devices.
-
Disposal Protocols: Develop clear protocols for the disposal of electronic devices and storage media.
In Conclusion
Securing sensitive information in government offices is an ongoing effort that demands vigilance and dedication. By establishing a strong information security policy, securing physical access, providing employee training and awareness, implementing robust network security, and following best practices for mobile devices and remote work, government agencies can significantly reduce the risk of data breaches and cyberattacks.
In an era where digital threats are constantly evolving, a proactive approach to data security is not just a recommendation but a necessity. By prioritizing data security, government offices can fulfill their responsibilities to protect national interests, citizens' privacy, and sensitive information effectively. Templeton Safes stands ready to support government agencies in their mission to safeguard their most valuable assets – sensitive data.